Berkeley Packet Filter Cheat Sheet - Berkeley packet filters are a raw interface to data link layers and are a powerful tool for intrusion detection analysis. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis. Probe[,probe,.] /filter/ { action } the probe specifies what events to instrument, the filter is optional and can filter down the events based. Udp src net xxx.xxx.xxx && dst host xxx.xxx.xxx.xxx Learn how to use bpf expressions to filter packets based on various criteria, such as host, net, port, proto, dir, and arithmetic. Use bpf filtering to quickly reduce large packet captures. Berkeley packet filters are a.
Udp src net xxx.xxx.xxx && dst host xxx.xxx.xxx.xxx Use bpf filtering to quickly reduce large packet captures. Berkeley packet filters are a. Berkeley packet filters are a raw interface to data link layers and are a powerful tool for intrusion detection analysis. Learn how to use bpf expressions to filter packets based on various criteria, such as host, net, port, proto, dir, and arithmetic. Probe[,probe,.] /filter/ { action } the probe specifies what events to instrument, the filter is optional and can filter down the events based. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis.
Learn how to use bpf expressions to filter packets based on various criteria, such as host, net, port, proto, dir, and arithmetic. Berkeley packet filters are a raw interface to data link layers and are a powerful tool for intrusion detection analysis. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis. Use bpf filtering to quickly reduce large packet captures. Berkeley packet filters are a. Udp src net xxx.xxx.xxx && dst host xxx.xxx.xxx.xxx Probe[,probe,.] /filter/ { action } the probe specifies what events to instrument, the filter is optional and can filter down the events based.
BPF resources FortiNDR Cloud 2023.2.0
Learn how to use bpf expressions to filter packets based on various criteria, such as host, net, port, proto, dir, and arithmetic. Berkeley packet filters are a. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis. Berkeley packet filters are a raw interface to data link layers and are a powerful tool for intrusion detection analysis. Use.
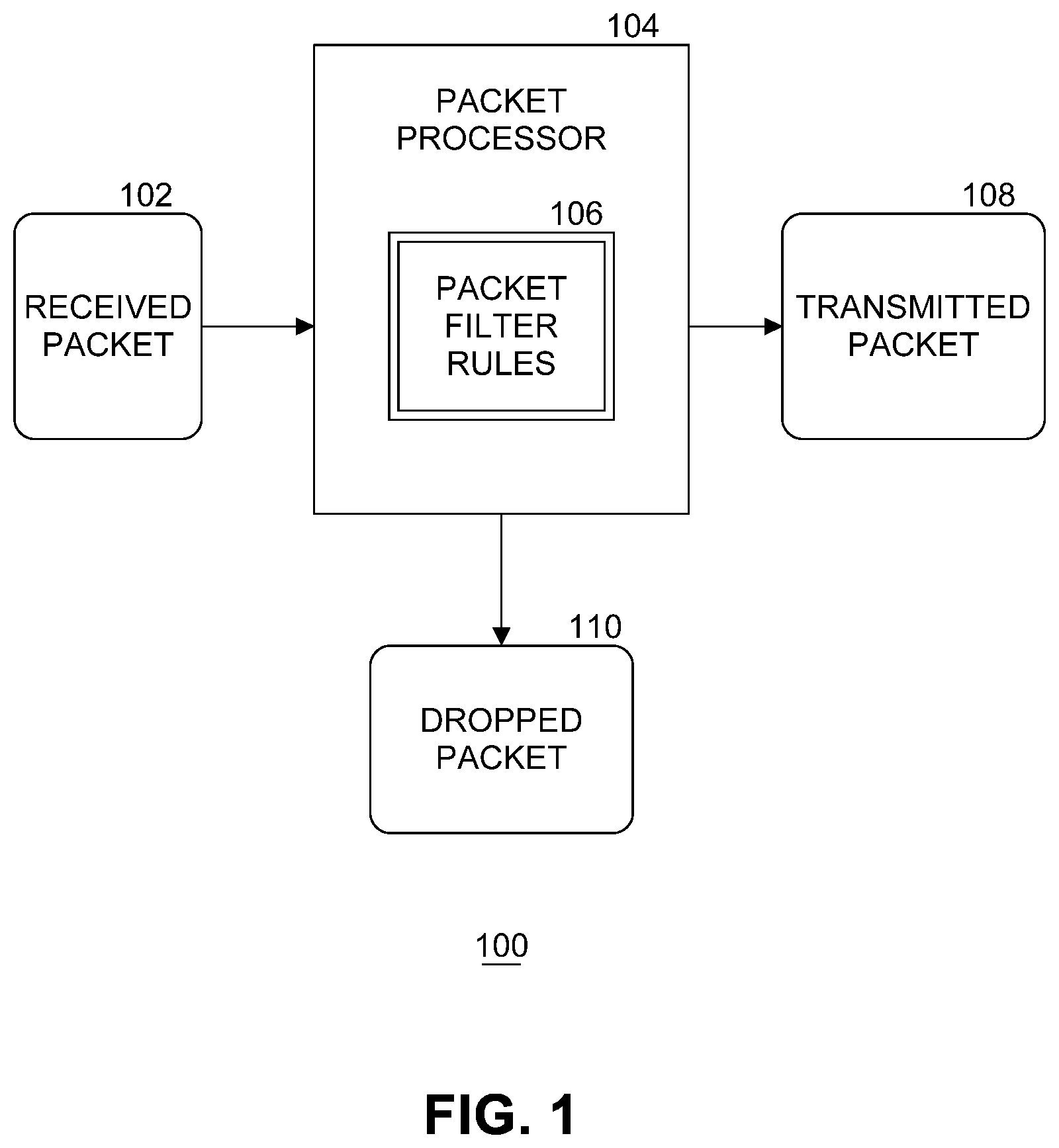
Extending berkeley packet filter semantics for hardware offloads Patent
Learn how to use bpf expressions to filter packets based on various criteria, such as host, net, port, proto, dir, and arithmetic. Udp src net xxx.xxx.xxx && dst host xxx.xxx.xxx.xxx Berkeley packet filters are a raw interface to data link layers and are a powerful tool for intrusion detection analysis. Use bpf filtering to quickly reduce large packet captures. Probe[,probe,.].
Configuration Driven Event Tracing with Traceleft and eBPF Speaker Deck
Berkeley packet filters are a. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis. Udp src net xxx.xxx.xxx && dst host xxx.xxx.xxx.xxx Probe[,probe,.] /filter/ { action } the probe specifies what events to instrument, the filter is optional and can filter down the events based. Berkeley packet filters are a raw interface to data link layers and.
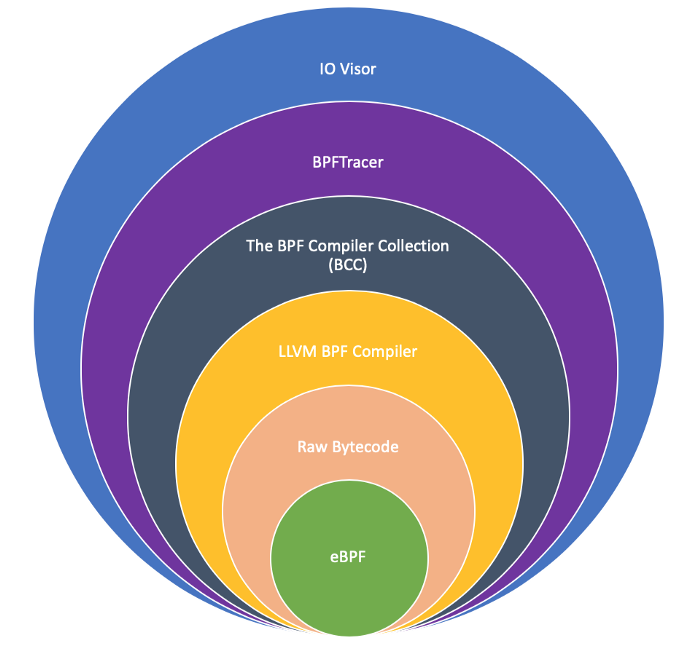
GitHub mikeroyal/eBPFGuide eBPF (extended Berkeley Packet Filter
Probe[,probe,.] /filter/ { action } the probe specifies what events to instrument, the filter is optional and can filter down the events based. Berkeley packet filters are a raw interface to data link layers and are a powerful tool for intrusion detection analysis. Berkeley packet filters are a. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis..
GitHub mikeroyal/eBPFGuide eBPF (extended Berkeley Packet Filter
Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis. Udp src net xxx.xxx.xxx && dst host xxx.xxx.xxx.xxx Learn how to use bpf expressions to filter packets based on various criteria, such as host, net, port, proto, dir, and arithmetic. Berkeley packet filters are a raw interface to data link layers and are a powerful tool for intrusion.
GitHub mikeroyal/eBPFGuide eBPF (extended Berkeley Packet Filter
Udp src net xxx.xxx.xxx && dst host xxx.xxx.xxx.xxx Probe[,probe,.] /filter/ { action } the probe specifies what events to instrument, the filter is optional and can filter down the events based. Berkeley packet filters are a. Learn how to use bpf expressions to filter packets based on various criteria, such as host, net, port, proto, dir, and arithmetic. Use bpf.
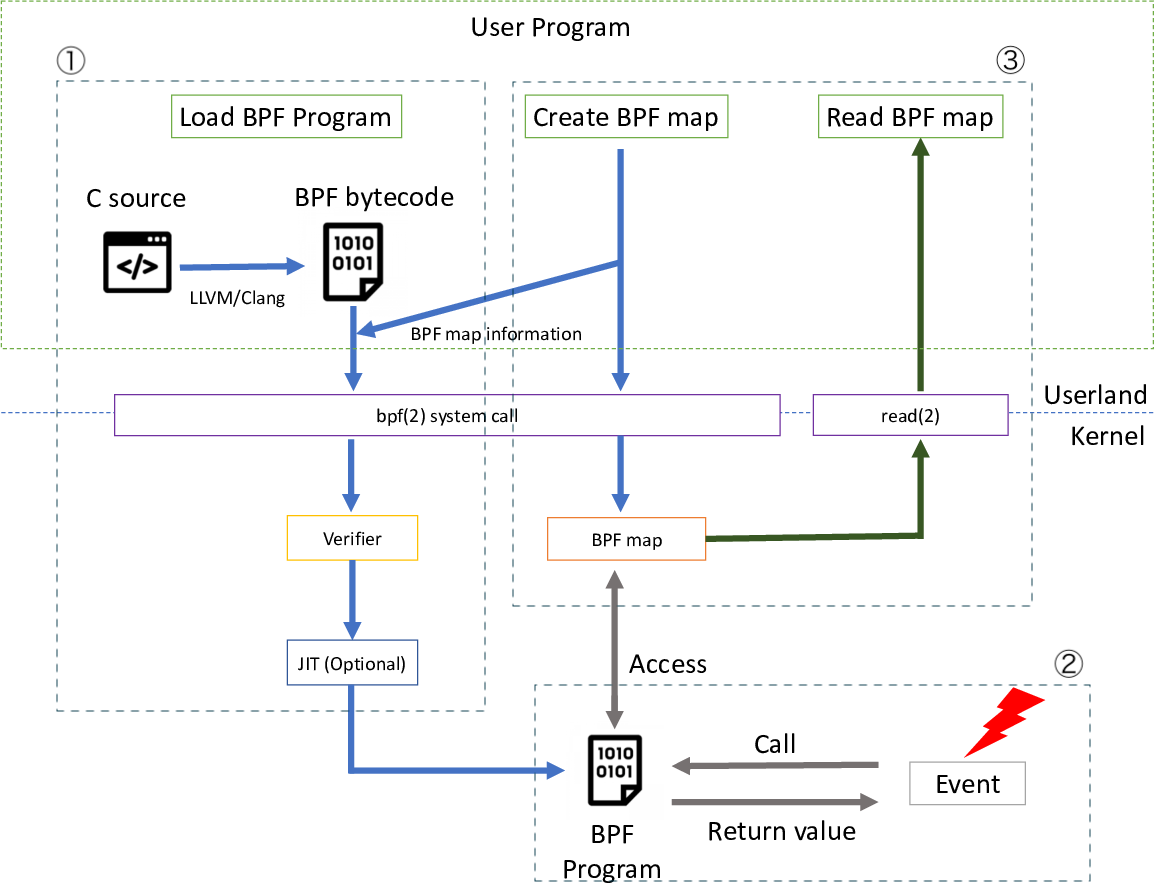
BPF (Berkeley Packet Filter)的简单介绍(一)CSDN博客
Berkeley packet filters are a. Udp src net xxx.xxx.xxx && dst host xxx.xxx.xxx.xxx Learn how to use bpf expressions to filter packets based on various criteria, such as host, net, port, proto, dir, and arithmetic. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis. Berkeley packet filters are a raw interface to data link layers and are.
featuredimagebpf.jpg
Use bpf filtering to quickly reduce large packet captures. Udp src net xxx.xxx.xxx && dst host xxx.xxx.xxx.xxx Berkeley packet filters are a. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis. Berkeley packet filters are a raw interface to data link layers and are a powerful tool for intrusion detection analysis.
Extended Berkeley Packet Filter (eBPF) Manoj Gupta’s Blog
Probe[,probe,.] /filter/ { action } the probe specifies what events to instrument, the filter is optional and can filter down the events based. Learn how to use bpf expressions to filter packets based on various criteria, such as host, net, port, proto, dir, and arithmetic. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis. Berkeley packet filters.
LinuxのBPFで何ができるのか? BPFの「プログラムタイプ」とは (1/2):Berkeley Packet Filter(BPF)入門
Berkeley packet filters are a raw interface to data link layers and are a powerful tool for intrusion detection analysis. Use bpf filtering to quickly reduce large packet captures. Learn how to use bpf expressions to filter packets based on various criteria, such as host, net, port, proto, dir, and arithmetic. Berkeley packet filters are a. Probe[,probe,.] /filter/ { action.
Udp Src Net Xxx.xxx.xxx && Dst Host Xxx.xxx.xxx.xxx
Berkeley packet filters are a. Use bpf filtering to quickly reduce large packet captures. Berkeley packet filters are a raw interface to data link layers and are a powerful tool for intrusion detection analysis. Probe[,probe,.] /filter/ { action } the probe specifies what events to instrument, the filter is optional and can filter down the events based.
Learn How To Use Bpf Expressions To Filter Packets Based On Various Criteria, Such As Host, Net, Port, Proto, Dir, And Arithmetic.
Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis.